How Poor Email Management Increases Phishing Risk in Law Firms

A phishing email works best when the recipient is overwhelmed, scanning fast, and unsure what normal looks like.
For most law firms, that’s just a Tuesday.
Attorneys manage hundreds of emails a week — clients, matters, opposing counsel, vendors.
An email arrives: opposing counsel, urgent, requesting a change to wire instructions before tomorrow’s closing. It looks right. The name is familiar. There’s no time to dig.
When none of it is organized by matter or consistently filed, that email doesn’t stand out. A spoofed sender looks like every other contact in a crowded inbox.
That’s the environment phishing is built to exploit. In this article, we break down the specific ways poor email management increases phishing risk at law firms and what better practices look like.
Just here for the list of legal AI tools? Skip ahead to the full roundup.
In This Article
- Law Firms Are a Prime Target — and Phishing Is the Front Door
- The Connection Between Email Chaos and Security Exposure
- Specific Ways Poor Email Management Raises Phishing Risk
- Business Email Compromise: The Costliest Phishing Variant for Law Firms
- Better Email Management Is Also a Security Strategy
- How an Integrated DMS Reduces Email Risk at the Structural Level
- FAQ
Law Firms Are a Prime Target — and Phishing Is the Front Door
Law firms are uniquely exposed. They hold privileged client communications that can’t be disclosed, manage active transactions where timing and instructions matter, and conduct most of that work over email.
That operational risk pattern makes phishing exceptionally effective.
Cybercriminals don’t need to breach a bank when they can breach the firm handling the bank’s acquisition.
Phishing is the most common entry point.
According to the ABA’s annual cybersecurity surveys, a significant and growing share of law firms report having experienced a security breach — and phishing and email-based attacks are consistently among the leading causes of law firm security breaches.
The Verizon Data Breach Investigations Report similarly identifies phishing as one of the top attack vectors across professional services.
The risk isn’t abstract.
Wire transfers, settlement funds, escrow instructions — all communicated largely over email, often under deadline pressure. When the workflow is that email-dependent, a single convincing message is all it takes.
The Connection Between Email Chaos and Security Exposure
Phishing succeeds because recipients are busy, overloaded, and scanning instead of reading.
A well-crafted phishing email only needs to be good enough to pass a two-second glance. In an inbox with 400 unread messages, that’s not a high bar.
When email isn’t organized by matter or client, attorneys have no baseline for what normal looks like.
Consider a request that arrives mid-afternoon from a familiar client name, asking to update wire instructions before a closing.
In an organized matter file, an attorney can check prior correspondence in seconds — confirm the sender’s address, review how the client typically communicates, verify whether this kind of request has ever come through before.
In an unmanaged inbox, none of that is quick.
They can’t easily answer: has this person emailed us before? Does this request match anything on this matter? Is this how this client typically communicates?
Without that context, a spoofed sender looks like any other new message in a crowded queue.
That’s the mechanism.
- Phishing exploits the gap between volume and attention.
- Disorganized email widens that gap — and law firms, with their high transaction volume and multi-party communications, are especially exposed.
The conditions phishing requires and the conditions an unmanaged inbox creates are effectively the same list.
| What Phishing Needs | What an Unmanaged Inbox Provides |
|---|---|
| Recipient scanning, not reading | Hundreds of unread, unfiled emails |
| No baseline for normal communication | No matter-based organization or filing |
| Urgency that discourages verification | Constant volume that normalizes urgency |
| Sender identity that goes unquestioned | No way to quickly cross-reference prior contact |
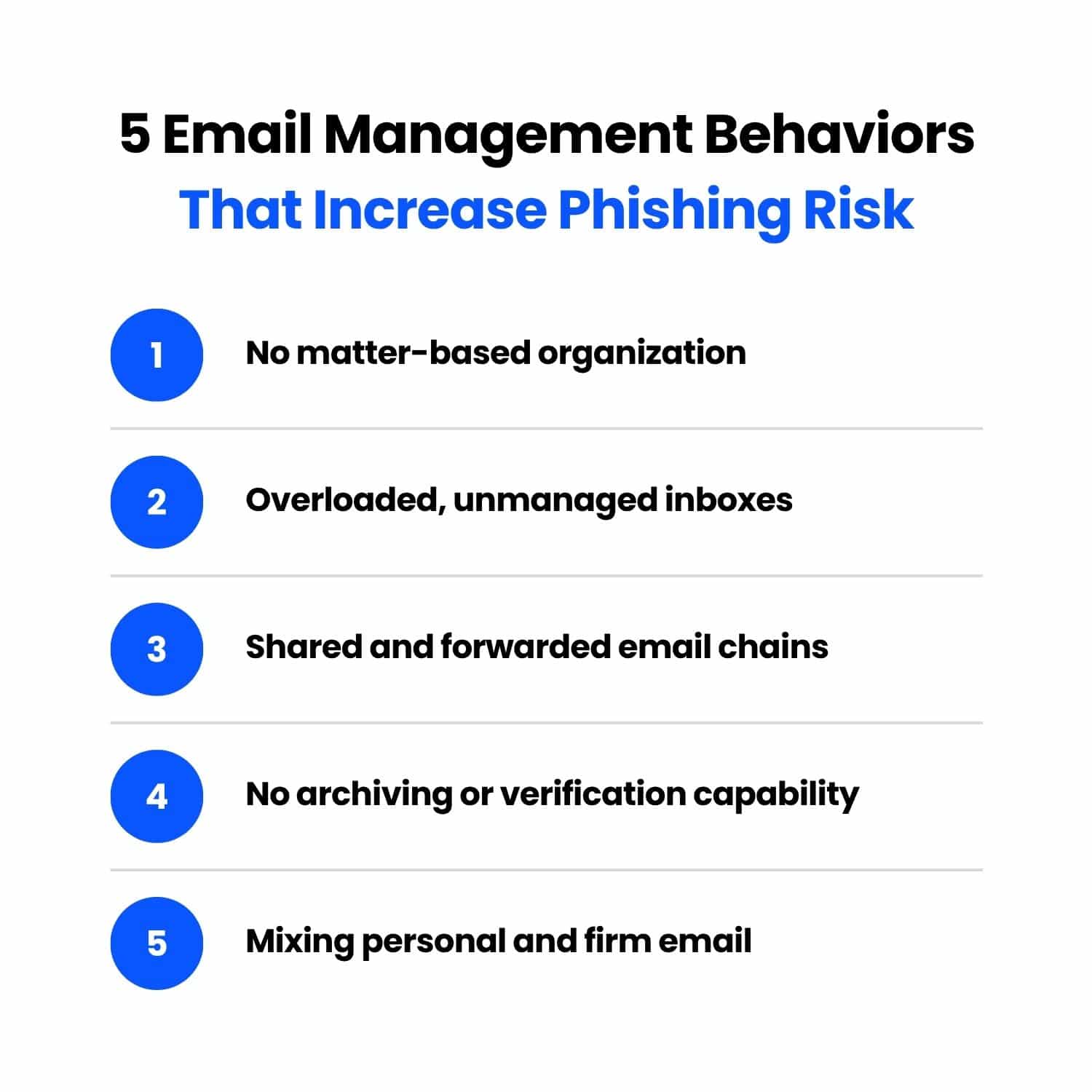
Specific Ways Poor Email Management Raises Phishing Risk
These aren’t edge cases or worst-case scenarios. They’re the everyday conditions that make phishing easier to execute and harder to catch — and they show up consistently as common document management mistakes law firms make.
No Matter-Based Organization Makes Sender Spoofing Harder to Catch
When email is filed by matter, attorneys develop a natural familiarity with how clients and counterparties communicate — their tone, their typical requests, their contact patterns.
That familiarity is a detection layer. Without matter-based organization, it doesn’t exist.
A spoofed email from “opposing counsel” or a “client” requesting urgent action lands in a general inbox alongside everything else.
Nothing flags it as unusual, and it gets the same two-second scan as every other message.
Overloaded Inboxes Create Urgency Fatigue
Phishing emails are engineered around urgency.
- "Wire funds by end of day."
- "Confirm your credentials immediately."
- "This matter requires your attention now."
Urgency overrides scrutiny.
In an unmanaged inbox where every day already feels urgent, a fraudulent request doesn’t register as out of place. Attorneys are operating in triage mode by default — phishing just takes advantage of it.
Shared and Forwarded Email Chains Obscure the Actual Sender
By the time an email has been forwarded two or three times, the visible sender field often reflects the last person who touched it, not the origin. An attorney sees a familiar colleague’s name, assumes the thread is legitimate, and acts on instructions that were injected several forwards back.
Shared mailboxes compound the problem.
When multiple people access the same inbox without clear ownership or filing protocols, nobody has full context on a thread. Nobody knows who already responded, who verified the sender, or whether anyone did either.
Spoofed senders thrive in that ambiguity.
No Archiving Policy Means Staff Can't Verify Past Correspondence
When a client — or someone posing as one — sends a wire transfer request, the fastest verification is checking prior correspondence.
You can ask yourself: does this match how they’ve communicated before? Have we confirmed these instructions in writing?
Firms with matter-based archiving can answer those questions in seconds. Firms without it often can’t answer them at all.
That gap is where wire fraud happens.
Mixing Personal and Firm Email Compounds the Risk
At smaller firms, attorneys routinely handle client communication through personal Gmail or Outlook accounts. The convenience is understandable.
When that happens, the firm loses visibility into those communications, retention and archiving fall outside any policy, and there’s no administrator oversight if something goes wrong.
A compromised personal account exposes client correspondence the firm didn’t know existed. By the time anyone finds out, the damage is already done.
Business Email Compromise: The Costliest Phishing Variant for Law Firms
Business Email Compromise (BEC) is phishing with a specific financial objective.
An attacker impersonates a client, opposing counsel, or vendor — often using a spoofed or compromised email account — and issues instructions designed to redirect a wire transfer or payment.
BEC Wire Transfer Request
From: michael.chen@harrisonfieldingllp.com
To: j.murphy@murphyandassociates.com
Subject: RE: Greenfield Closing — Updated Wire Instructions
Janet,
Hope you’re well. Quick update before tomorrow’s closing — our accounting department flagged an issue with the wire instructions we sent last week. Please use the updated details below for the Greenfield disbursement:
Bank: First National Bank Account: 847392015 Routing: 021000089
Let me know once the transfer is confirmed. We’re on a tight timeline with the seller.
Thanks, Michael Chen Harrison Fielding LLP
The email looks legitimate. The sender appears familiar. The request fits the context of an active matter.
By the time anyone realizes something is wrong, the funds are gone.
Law firms are a preferred BEC target for an obvious reason: they move money. Settlement funds, escrow disbursements, real estate closings, client trust accounts — large transactions conducted primarily over email, often under time pressure.
That combination makes the fraudulent wire request an exceptionally effective attack.
The FBI’s IC3 reports consistently rank BEC among the highest-loss cybercrime categories, with reported losses of about $3.05 billion in 2023, $2.77 billion in 2024, and $2.95 billion in 2025.
For individual firms, a single successful attack can mean a six-figure loss with little realistic path to recovery.
Firms with real estate practices, active litigation, or trust accounting are especially exposed — these are high-volume, deadline-driven transaction types where an urgent wire request doesn’t raise immediate flags.
Better Email Management Is Also a Security Strategy
Most law firms approach email security as a technology problem — spam filters, MFA, endpoint protection. Those controls matter.
But they don’t address what happens inside the inbox once an email gets through.
Structured email management closes that gap.
When attorneys file email by client and matter, they build the context needed to spot anomalies. An unexpected wire request from a familiar client stands out when you can see the full history of how that client actually communicates.
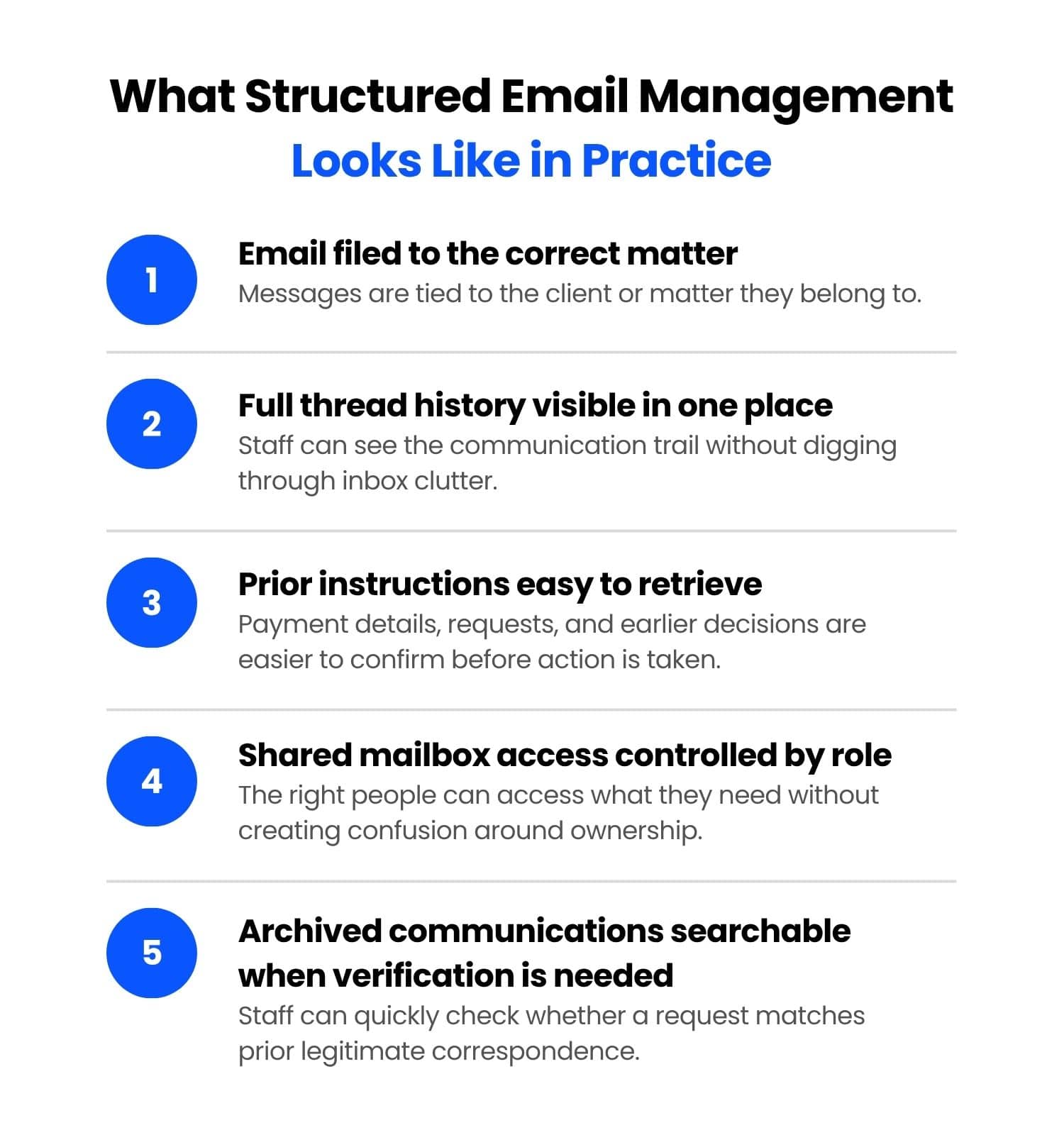
A few practices make a measurable difference:
- Matter-based email filing. Every client communication filed to the relevant matter, not left in a general inbox. Attorneys can cross-reference prior correspondence quickly when something looks off.
- Clear inbox protocols. Defined expectations for how email is handled, filed, and followed up on — across the whole firm, not just individual attorneys.
- Consistent archiving. Email that's archived and retrievable means verification is possible, and it’s the foundation of secure document storage for any firm handling sensitive client communications.
- Role-based access to shared mailboxes. Shared inboxes without access controls create visibility gaps. Limiting access by role reduces both exposure and confusion around thread ownership.
None of this replaces technical security controls. Structured email management makes those controls more effective by reducing the chaos that phishing depends on.
How an Integrated DMS Reduces Email Risk at the Structural Level
The email management practices covered in this article — matter-based filing, consistent archiving, clear inbox protocols — are meaningful on their own. An integrated document management system makes them easier to sustain across the whole firm.
When email is managed inside a document management system (DMS) like LexWorkplace, attorneys file communications directly to the relevant matter from Outlook. Every email is searchable, archived, and connected to the client file it belongs to. Beyond an organizational improvement, it removes the inbox chaos that phishing depends on.
Disorganized email gives phishing attacks a place to land. Structured email management — supported by the right tools — takes that away.
If you’re not sure where your firm stands, a free document and email audit is a practical starting point.
FAQ
Law firms hold high-value, sensitive information — client financials, privileged communications, and transaction data — and regularly handle large wire transfers and settlement funds. That combination of sensitive data and financial transactions makes them an attractive and high-yield target for phishing and business email compromise attacks.
Disorganized email removes the context attorneys need to spot suspicious messages.
When email isn’t filed by matter, there’s no baseline for how clients and counterparties normally communicate. Overloaded inboxes create urgency fatigue, forwarded chains obscure sender identity, and the absence of archiving makes it impossible to verify whether a request is legitimate.
Business email compromise (BEC) is a phishing variant where an attacker impersonates a trusted contact — a client, vendor, or opposing counsel — to redirect a wire transfer or payment. Law firms are a primary target because they routinely move large sums of money over email. A single successful BEC attack can result in a six-figure loss with little realistic path to recovery.
Effective email management for security includes matter-based filing, consistent archiving, clear inbox protocols, and role-based access to shared mailboxes. These practices give attorneys the context and verification capability needed to identify suspicious requests before acting on them.
A document management system (DMS) that integrates with email allows attorneys to file, search, and archive communications by matter directly from Outlook. This removes inbox chaos, creates a verifiable record of prior correspondence, and gives the firm visibility and structure that makes spoofed or fraudulent emails easier to identify.
Looking for Document Management Software?
LexWorkplace:
Modern Document Management for Law Firms
LexWorkplace is document & email management software, born in the cloud and built for law firms. Here’s a quick primer on how it works, or get your free trial to discover LexWorkplace for yourself.
Organize by Client & Matter
Organize documents, email and notes by client or matter. Store and manage all data for a case or project in one place.
Go Beyond Basic Files & Folders
Supercharge your firm’s productivity with true DMS functions.
- Version Management
- Document Tagging & Profiling
- Document Check-Out / Check-In
- Microsoft Office Integration
- Automatic, Integrated OCR
- Convert Word Docs to PDF
Search Everything
LexWorkplace is like Google for your law firm. Search across millions of pages, documents, folder email and notes in seconds. Refine your search by matter, document type, author and more.
Search by…
- Client or Matter
- Document Type (Contract, Complaint, Order, etc.)
- Document Status (Draft, Final, etc.)
- Document Tags (Filed With Court, Fully Executed, etc.)
Outlook Integration + Comprehensive Email Management
Save emails to a matter without leaving Outlook. Saved emails are accessible to your entire team, organized and searchable.
- Outlook Add-In that Works With Windows and Macs
- Save Entire, Original Email to a Matter in a LexWorkplace
- Email De-Duplication
- Organize Emails into Folders, Subfolders
Works with Windows and Macs
All of LexWorkplace is compatible with both Windows and Mac computers.
Next Steps
See What Clients Have to Say
Lawyers love LexWorkplace. See how the system streamlined one lawyer’s practice.
Watch the 5-Minute Demo
See LexWorkplace in action in our quick 5-minute overview and demonstration.
Or, if you want a one-on-one demo, or want to talk about LexWorkplace for your firm, schedule a call or demo below.
You Might Also Like
May 24, 2026
How Email Search Works in Legal Document Management Systems
Learn how email search works in a legal…
May 5, 2026
Why Email and Document Management Should Be Integrated for Law Firms
Learn why law firms should manage email…
Want More Legal Technology Tips?
Subscribe to Uptime Legal to get the latest legal tech tips and trends, delivered to your inbox weekly.